Are Your Assets—and Their Weak Points—Ready for a Quantum Future?
Author

Quantum computing is about to change everything for the payments industry! Today’s cryptography protocols protect against most threats; however, quantum computing will be capable of breaking these math-based algorithms in a matter of seconds. Because payments data is high value and heavily regulated, a data breach within the payments ecosystem can result in substantial material damages, reputational loss, and legal liability.
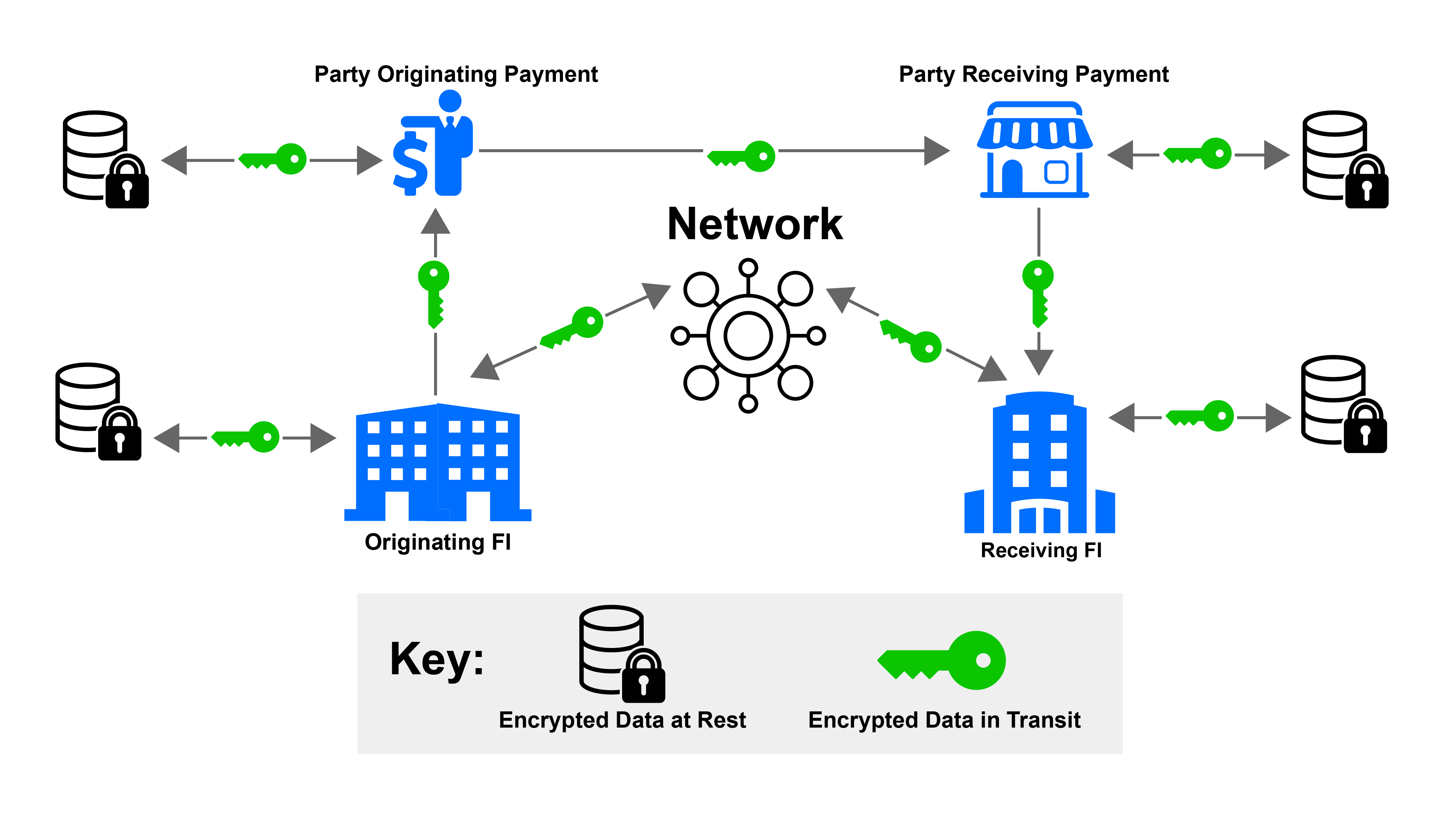
Each payments participant has a role in securing transactions and data, as illustrated in this model.
Your organization should have already started learning about the impacts of quantum computing on the payments infrastructure and incorporating that knowledge into its strategic planning. But do you know what data and applications are most critical to your operations, and what the greatest threats to their security are?
It is imperative to include a comprehensive inventory of your most critical data and assets (the “crown jewels”) that use public-key cryptography, and to assess the magnitude of vulnerabilities that will inform your quantum readiness priorities.
Identifying & Prioritizing the Crown Jewels
Considering both technical and business perspectives, your organization’s crown jewels typically fall into the categories of inventory, data, applications and systems, and policies and procedures. Prioritization will be determined based on the criticality to your operations and level of vulnerability threat.
Learn more about quantum-safe payments in the paper, "Protecting Payments
in the Quantum Era: Setting a Course for Action," published by the Nacha Payments Innovation Alliance Quantum Payments Project Team.








